Chief Security Officer (CSO) Mastery Guide
🏁 Chapter 1: The Role of a Chief Security Officer
- 🧠 Core Responsibilities
- 🔒 Overseeing Security Operations
- 📘 Developing Security Strategies
- 🏁 Risk Management & Mitigation
- 🤝 Leadership & Collaboration
- 🧩 Coordinating with Executives & IT Teams
- 🏁 Managing Security Personnel
- 🔍 Reporting to the CEO & Board
🛡️ Chapter 2: Physical Security Management
- 🏢 Facility & Infrastructure Security
- 🛠️ Surveillance Systems (CCTV, Sensors)
- 🚪 Access Control & Badge Systems
- 🔔 Alarm & Intrusion Detection
- 🧠 Incident Response & Emergency Planning
- 📘 Emergency Protocols (Fire, Evacuation)
- 🏁 Disaster Recovery Plans
- 🚀 Security Drills & Training
🖥️ Chapter 3: Cybersecurity & Digital Protection
- 🔍 Cyber Threat Prevention
- 🛠️ Network Security & Firewalls
- 🏁 Threat Detection Systems
- 📊 Vulnerability Assessments
- 🧠 Incident Management
- 📘 Cyberattack Response Protocols
- 🏁 Data Breach Containment
- 🚀 Forensic Investigations
📊 Chapter 4: Risk Assessment & Threat Analysis
- 🛠️ Identifying Threats
- 🔍 Internal & External Threats
- 🏁 Industry-Specific Risks
- 📊 Historical Incident Data
- 🧠 Evaluating Risk Impact
- 🏷️ Financial & Reputational Risks
- 📘 Supply Chain Vulnerabilities
- 🏁 Compliance & Legal Risks
🏗️ Chapter 5: Security Strategy & Policy Development
- 📘 Policy Frameworks
- 🛠️ Access Control Policies
- 🚀 Data Encryption Standards
- 🏁 Employee Security Protocols
- 🧠 Strategy Execution
- 📊 Security Roadmap Creation
- 🏁 Budgeting & Resource Allocation
- 🔍 Technology & Vendor Selection
🔓 Chapter 6: Identity & Access Management (IAM)
- 🧠 User Access Controls
- 🚪 Role-Based Access (RBAC)
- 🏁 Single Sign-On (SSO) Solutions
- 🔍 Multi-Factor Authentication (MFA)
- 📊 Privileged Access Management (PAM)
- 🛠️ Admin & Superuser Controls
- 🏁 Session Monitoring & Audits
- 🚀 Least Privilege Principles
📘 Chapter 7: Security Awareness & Training
- 🧠 Employee Training Programs
- 🛠️ Phishing Awareness Workshops
- 📊 Social Engineering Simulations
- 🚀 Data Handling Best Practices
- 🏁 Building a Security Culture
- 🔍 Incident Reporting Channels
- 🧩 Gamified Learning Experiences
- 🏁 Continuous Learning & Updates
🔍 Chapter 8: Security Monitoring & Intelligence
- 🛡️ Real-Time Monitoring
- 🛠️ Security Operations Center (SOC)
- 📊 SIEM Tools & Log Analysis
- 🏁 Threat Hunting Teams
- 🚀 Threat Intelligence
- 🔍 Dark Web Monitoring
- 🏁 Information Sharing Networks
- 📘 Threat Reports & Alerts
📈 Chapter 9: Compliance & Legal Security Standards
- 🏁 Regulatory Frameworks
- 📘 GDPR, HIPAA, ISO 27001
- 🛠️ PCI DSS & Financial Security
- 🔍 National & Local Regulations
- 🧠 Audit & Reporting
- 🏗️ Security Audits & Assessments
- 📊 Compliance Documentation
- 🏁 Penetration Testing Reports
🚀 Chapter 10: Incident Response & Crisis Management
- 🔍 Incident Handling
- 🛠️ Creating an IR Plan
- 🏁 Defining Escalation Procedures
- 📘 Root Cause Analysis (RCA)
- 🧠 Post-Incident Recovery
- 🚀 Communication with Stakeholders
- 🏁 Lessons Learned & Improvement
- 📊 Updating Security Protocols
🏁 Chapter 11: Vendor & Third-Party Security Management
- 🧠 Vendor Risk Assessments
- 🛠️ Supply Chain Security Audits
- 🔍 Security Clause in Contracts
- 📘 Monitoring Third-Party Access
- 🚀 Partnership Management
- 🏁 Collaboration with Security Firms
- 📊 Managed Security Services (MSS)
- 🏷️ Continuous Vendor Evaluation
📢 Chapter 12: Security Innovation & Technology Trends
- 🚀 Emerging Tech
- 🛠️ AI-Powered Threat Detection
- 📘 Blockchain for Data Security
- 🔍 IoT Security Solutions
- 🏁 Future-Proofing Security
- 🧠 Adapting to New Threats
- 📊 Investing in R&D
- 🏗️ Partnering with Innovators
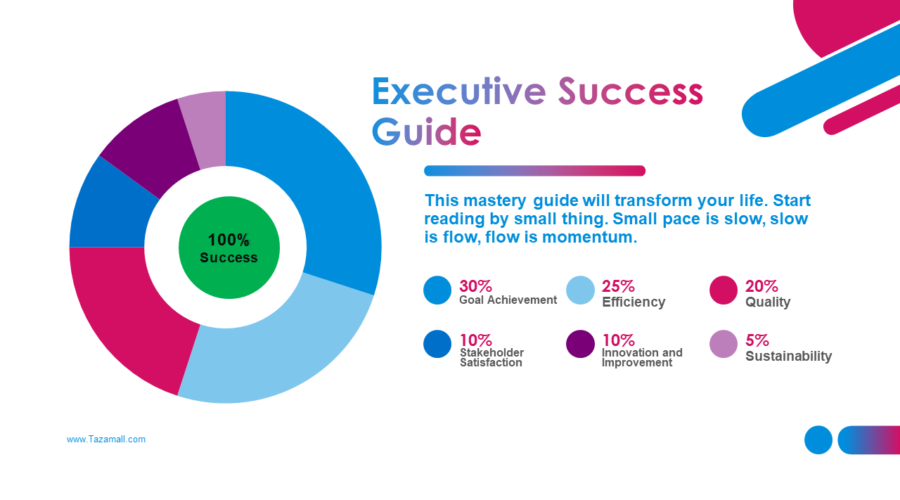
🧠 Chapter 13: Security Metrics & Performance Monitoring
- 📊 Defining Security KPIs
- 🏁 Incident Resolution Times
- 📘 Number of Detected Threats
- 🛠️ Employee Security Compliance
- 🔍 Continuous Improvement
- 🚀 Trend Analysis & Reports
- 🏁 Quarterly Security Reviews
- 📊 Adjusting Policies & Strategies
🎯 Chapter 14: Crisis Communication & Public Relations
- 📘 Internal & External Comms
- 🛠️ Communication Playbooks
- 🚀 Media & Press Handling
- 🏁 Customer Assurance Messaging
- 🏁 Reputation Management
- 🧠 Social Media Monitoring
- 📊 Rebuilding Public Trust
- 🔍 Transparency & Updates
🔐 Chapter 15: Leadership & Vision as a CSO
- 🧠 Becoming a Security Visionary
- 🚀 Inspiring Proactive Security Culture
- 📘 Balancing Risk & Innovation
- 🏁 Mentoring Future Security Leaders
- 🏗️ Long-Term Legacy
- 🛠️ Building Resilient Security Systems
- 📊 Knowledge Sharing & Thought Leadership
- 🔍 Shaping Industry Standards